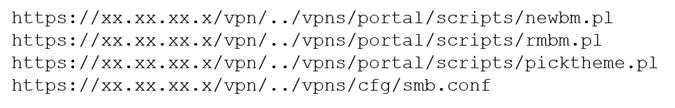
A penetration tester discovered a vulnerability that provides the ability to upload to a path via discovery traversal. Some of the files that were discovered through this vulnerability are:
Which of the following is the BEST method to help an attacker gain internal access to the affected machine?
- Edit the discovered file with one line of code for remote callback.
- Download .pl files and look for usernames and passwords.
- Edit the smb.conf file and upload it to the server.
- Download the smb.conf file and look at configurations.