A penetration tester gains access to a system and establishes persistence, and then run the following commands:
Which of the following actions is the tester MOST likely performing?
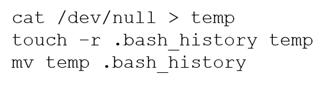
- Redirecting Bash history to /dev/null
- Making a copy of the user's Bash history to further enumeration
- Covering tracks by clearing the Bash history
- Making decoy files on the system to confuse incident responders
Answer(s): C
Reference:
https://null-byte.wonderhowto.com/how-to/clear-logs-bash-history-hacked-linux-systems-cover- your-tracks-remain-undetected-0244768/